AP Examples :: Chapter 14. Authentication Proxy :: Part VI: Managing Access Through Routers :: Router firewall security :: Networking :: eTutorials.org

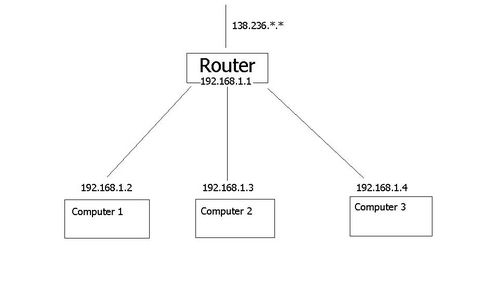
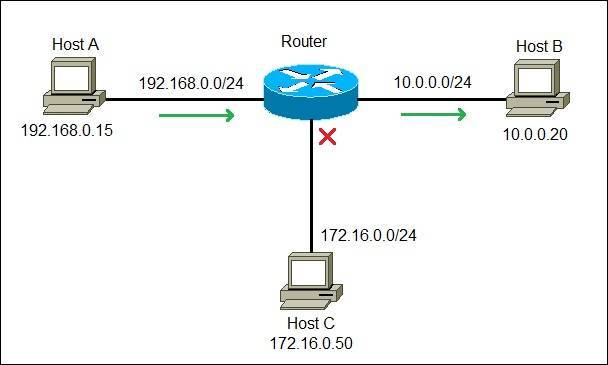
Lock-and-Key Example :: Chapter 13. Lock-and-Key Access Lists :: Part VI: Managing Access Through Routers :: Router firewall security :: Networking :: eTutorials.org
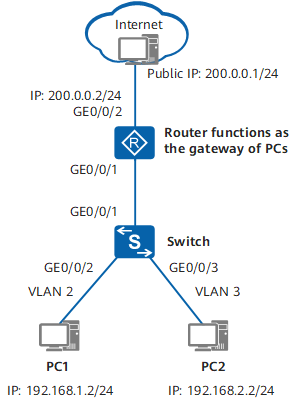
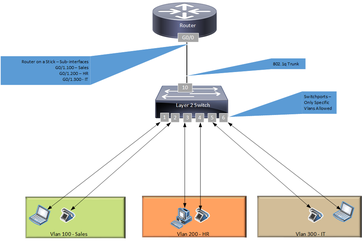
Example for Configuring a Layer 2 Switch to Work with a Router for Internet Access - Sx300 Series Switches Typical Configuration Examples - Huawei






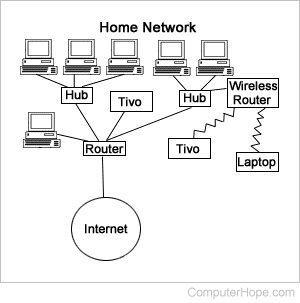

![OpenWrt Wiki] Routing example: IPv4 OpenWrt Wiki] Routing example: IPv4](https://openwrt.org/_media/docs/guide-user/network/ipv4.jpeg?w=800&tok=ed9f4b)